- Category
- Latest news
Inside The Alleged Hack That Exposed 10 Petabytes Of China’s Military Simulation Secrets
Hackers claim to have breached a major Chinese state-run computing facility and obtained up to 10 petabytes of sensitive data, including materials related to weapons testing and military simulations.
We bring you stories from the ground. Your support keeps our team in the field.
According to NetAskari, the data allegedly originates from the National Supercomputing Center in Tianjin, a key infrastructure site used for advanced scientific and defense-related calculations.

Initial reports about the dataset surfaced on dark web forums, where a user operating under the alias “airborneshark1” began offering access to the archive for sale.
According to reports on Substack, the group behind the breach—calling itself Flaming China—claimed responsibility and began promoting samples of the data online. The group has reportedly operated a Telegram channel since early February 2026.
❗️The leaked sample data from China's National Supercomputing Center in Tianjin includes a video of what seems to be a simulation of a bunker buster bomb, designed to penetrate bunkers and damage underground structures. https://t.co/AC2PmfTZTj pic.twitter.com/Br4vQqLCVi
— International Cyber Digest (@IntCyberDigest) March 19, 2026
According to NetAskari, the attackers are offering limited previews of the dataset for around $3,000, while full access is being marketed at significantly higher prices.
Independent analysts cited in reporting on the leak noted that some of the released samples appear consistent with authentic internal data, though no official confirmation from Chinese authorities has been provided regarding the full scope of the breach.

The National Supercomputing Center in Tianjin is a strategic state facility that supports high-performance computing tasks, including weather modeling, industrial simulations, and defense-related research. It is widely used by Chinese military contractors for virtual testing and engineering analysis, according to NetAskari.
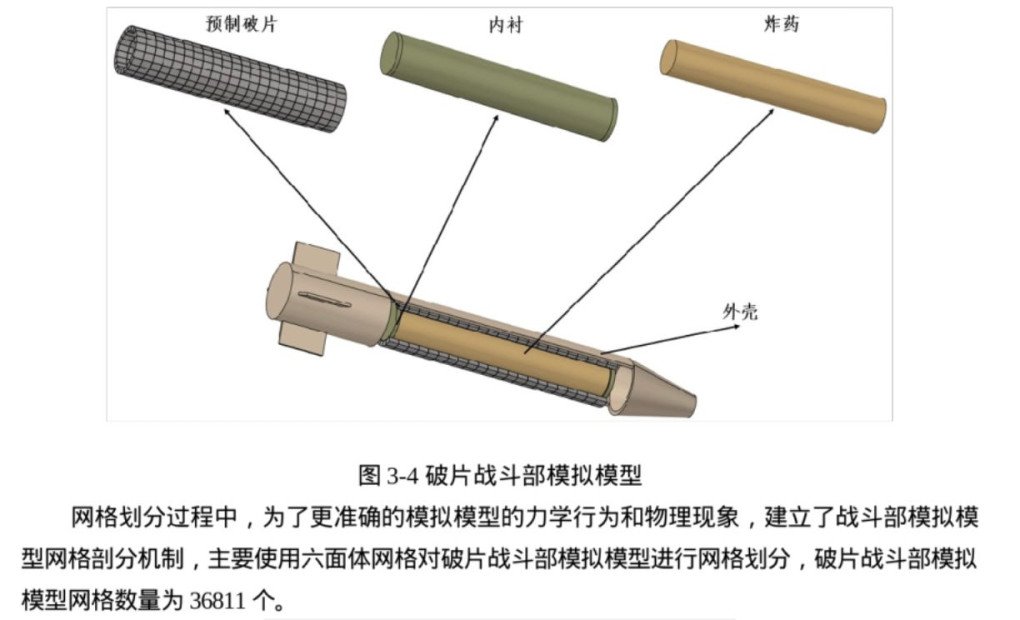
Samples of the leaked data reportedly include internal directory structures, user credentials, technical manuals, radar system test results, and simulation data involving weapons effects. Among the materials are documents labeled as classified for up to ten years.
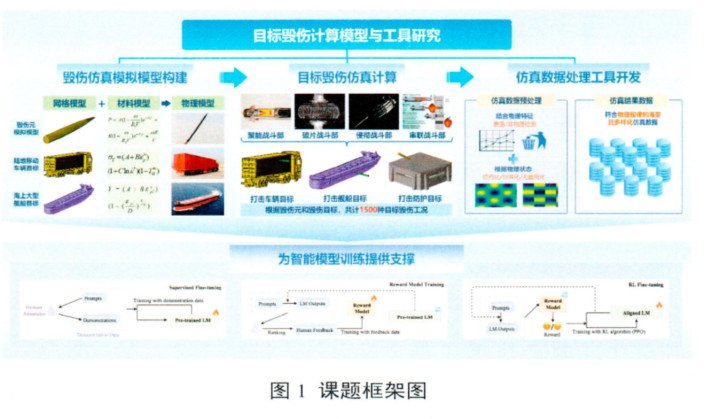
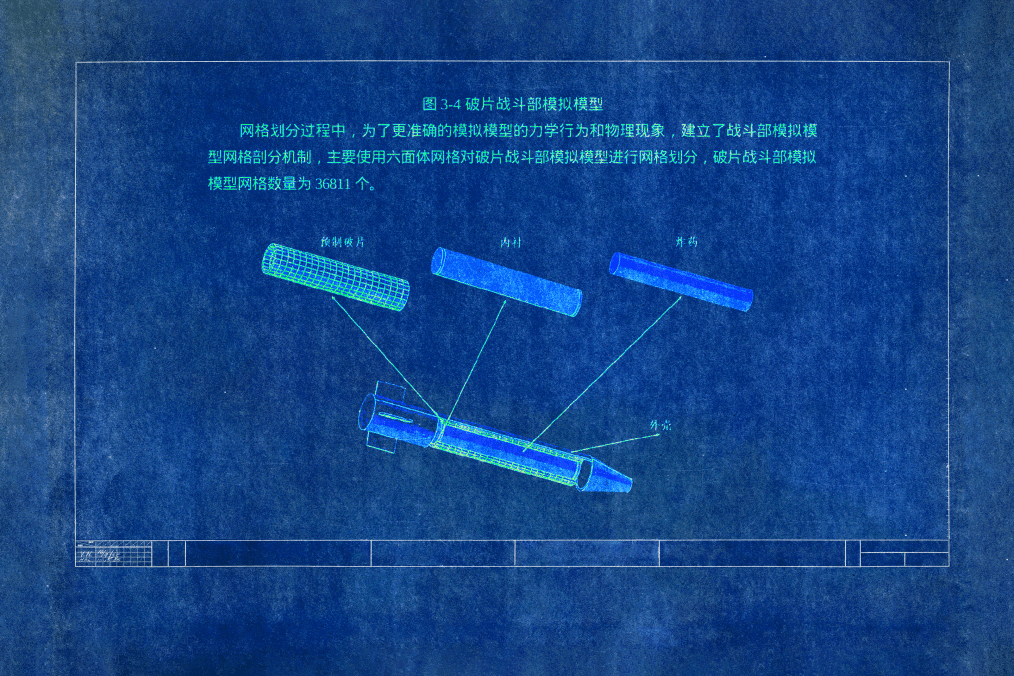
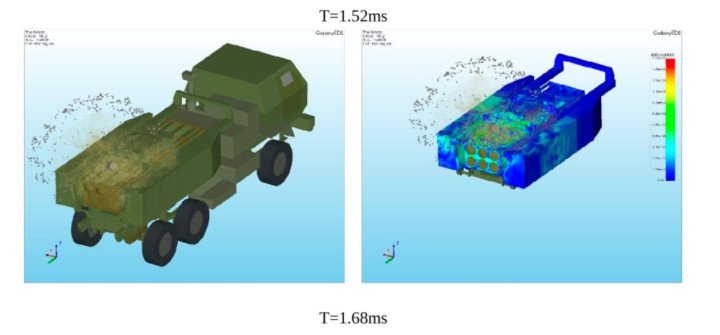
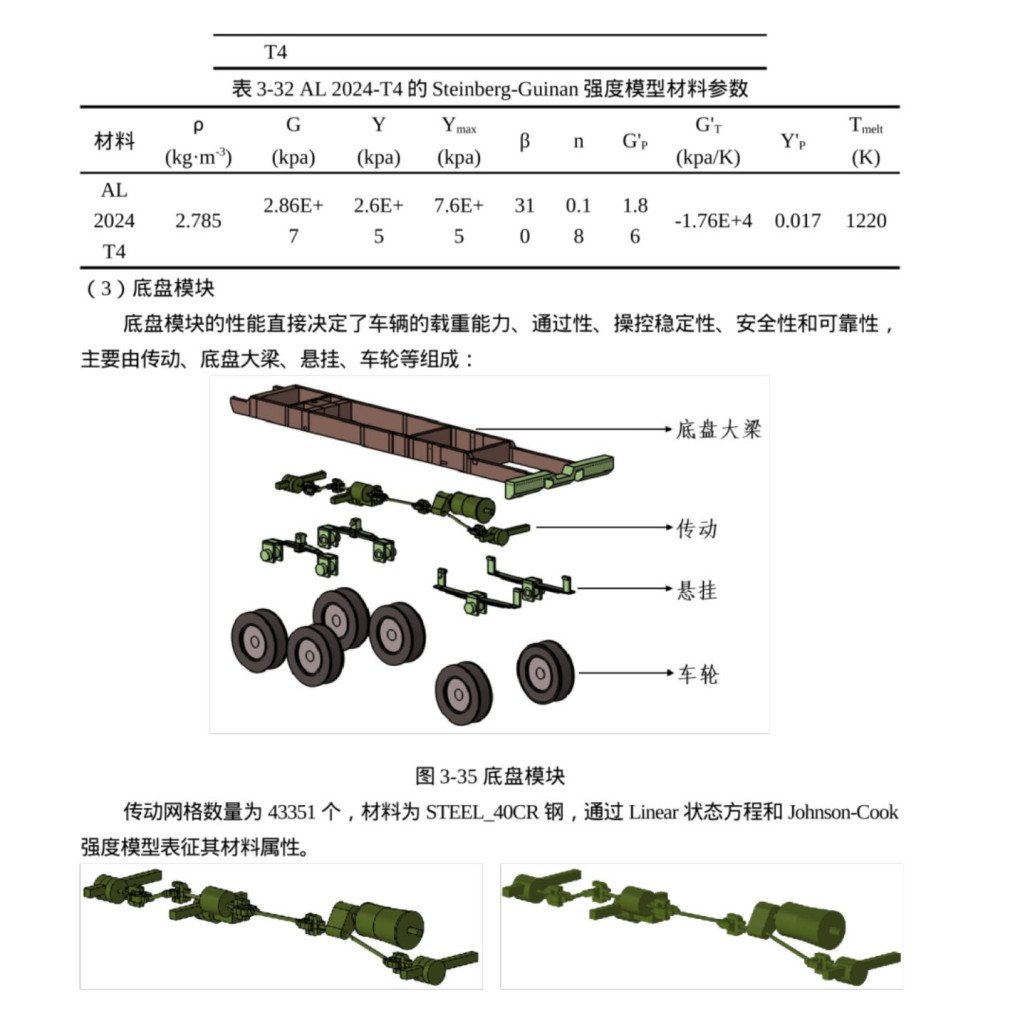
One 2025 report details testing of bunker-penetrating munitions and includes digital models simulating strikes on systems similar to the US HIMARS launcher. Other datasets reportedly focus on virtual attack simulations against aircraft carriers and hardened bunker structures, alongside animated visualizations of missile warhead testing processes.
Additional files are linked to a project labeled “Stealth,” which references systems such as the US X-47B unmanned aircraft and other advanced technologies. Analysts noted the presence of complex binary datasets and technical tables whose exact applications remain unclear.
According to analysts cited in reporting on the breach, the claimed volume of 10 petabytes raises questions about feasibility, as extracting such a large dataset without detection would likely require prolonged access to internal systems or potential insider involvement.
Shortly after reports of the leak emerged, Chinese authorities reportedly removed several senior figures linked to defense development programs, including Yang Wei, a chief designer associated with the J-20 fighter program.
Experts expect further investigation into the breach, as well as potential tightening of cybersecurity measures across sensitive Chinese research institutions, though the actual scale of the compromise remains unverified and the figure of 10 petabytes may be overstated.
Earlier, US President Donald Trump directed the Pentagon to prepare for a major restructuring of the armed forces aimed at deterring China and Russia. Defense Secretary Pete Hegseth said the administration had been tasked with rebuilding military capabilities and restoring deterrence, while Trump also accused China, Russia, and North Korea of coordinating actions against the United States.
Discuss this article:
-4a56a6b482ec132402c16ef6fcabf9a2.png)


-c439b7bd9030ecf9d5a4287dc361ba31.jpg)

-111f0e5095e02c02446ffed57bfb0ab1.jpeg)

