- Category
- Latest news
Israeli Software Used to Assassinate Ayatollah Khamenei Uncovered in Russian Surveillance Networks

Israeli video analytics software has been discovered operating within Russian video surveillance systems, The Moscow Times reported on March 13.
The same technology was reportedly used by intelligence agencies to track and assassinate Iranian Supreme Leader Ayatollah Ali Khamenei.
We bring you stories from the ground. Your support keeps our team in the field.
The software, known as BriefCam, is designed to rapidly analyze massive video streams, search for specific events in archives, and identify targeted human actions and vehicles. According to a Russian state news outlet, cited by The Moscow Times, the platform is currently active at several high-profile Russian facilities, including the Russian Academy of Sciences' Institute of Theoretical and Experimental Biophysics, the Eurasia skyscraper in the Moscow City business district, and the Zotov cultural center.
BriefCam was acquired by the Japanese corporation Canon in 2018 and subsequently integrated into the XProtect video management system developed by Denmark’s Milestone Systems. While Milestone Systems officially withdrew from the Russian market in 2022 following Russia’s full-scale invasion of Ukraine, the technology remains deeply embedded in the country.
Industry insiders told The Moscow Times that local distributors continue to supply and maintain the products through illicit “gray” import schemes or by installing cracked, pirated versions of the software.
The presence of this software raises severe security concerns in Moscow, given its alleged capabilities. It was previously reported that Israeli intelligence successfully hijacked Tehran’s traffic and surveillance cameras to gather critical reconnaissance on the movements of high-ranking Iranian officials.
Utilizing advanced AI algorithms to identify behavioral patterns and specific targets, the encrypted video feeds were reportedly beamed directly to servers in Tel Aviv and southern Israel.
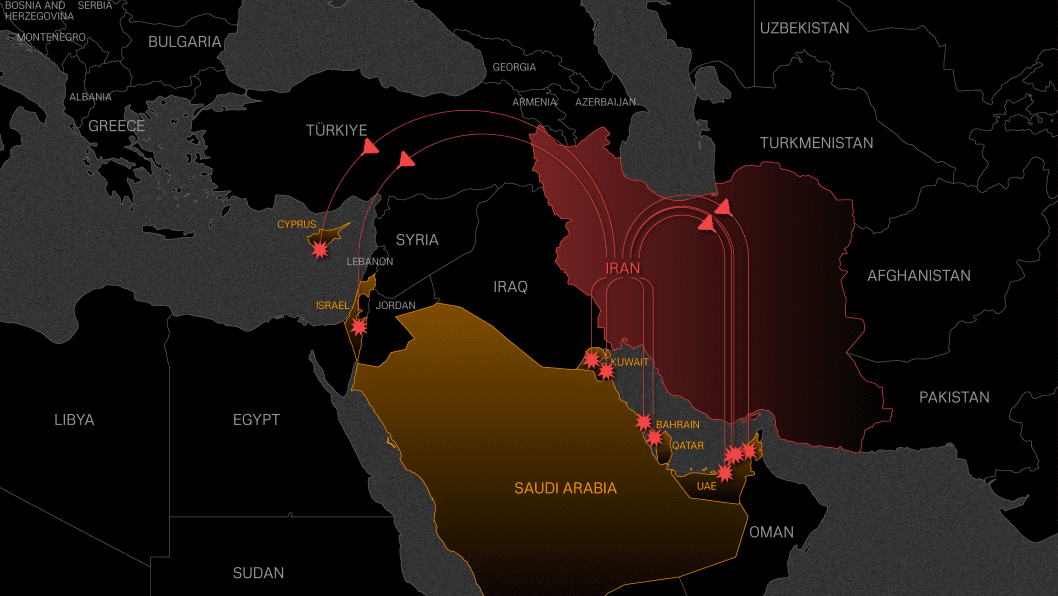
This digital infiltration was a crucial element in the recent decapitation strike against Iran’s leadership. The camera hack allowed Israeli operatives to map blind spots, monitor parking routines outside Khamenei’s residence on Pasteur Street, and thoroughly study the compound’s security protocols.
To ensure the strike’s success, mobile communication towers surrounding the complex were simultaneously disabled, completely paralyzing the Iranian security detail’s ability to share information or coordinate a response.
The discovery of this Israeli video analytics software on Russian servers highlights a much larger and systematic failure to prevent sensitive technology from slipping through the international sanctions net. Russia continues to aggressively bypass export controls by utilizing a sprawling network of intermediaries, shell companies, and third-country distributors operating out of jurisdictions like China, Hong Kong, and the United Arab Emirates.
This highly organized “gray” supply chain doesn’t just smuggle civilian software; it provides the critical hardware necessary to sustain Moscow’s war effort. Investigators had previously found that out of 1,119 distinct components identified inside Russia’s most advanced Su-34 and Su-35 fighter jets, a staggering 1,115 were manufactured by companies headquartered in the United States, Europe, and allied nations.
Just as local distributors have kept systems like BriefCam operational through pirated versions and illicit imports, Russia’s military-industrial complex remains heavily dependent on these back-channel networks to maintain its intelligence and precision strike capabilities.
Discuss this article:
-4a56a6b482ec132402c16ef6fcabf9a2.png)
-72b63a4e0c8c475ad81fe3eed3f63729.jpeg)

-c439b7bd9030ecf9d5a4287dc361ba31.jpg)


