- Category
- Latest news
Russia’s Nuclear Arsenal Is Hiding Secrets. Here’s What Newly Hacked Data Shows

Ukrainian cyber specialists and OSINT analysts obtained documents related to software tools used in the development and testing of Russia’s strategic nuclear forces, according to the investigative community InformNapalm on March 13.
We bring you stories from the ground. Your support keeps our team in the field.
The materials were reportedly acquired during a multi-stage cyber intelligence operation conducted by analysts from Ukrainian Militant, cyber specialists from the 256th Cyber Assault Division, and volunteers from the international intelligence community InformNapalm.
According to InformNapalm, the operation combined HUMINT, OSINT, and CYBINT techniques to obtain information that is not available through open sources. The data was reportedly collected during 2024 and subsequently shared with Ukraine’s Defense Forces before parts of it were disclosed publicly in 2026.

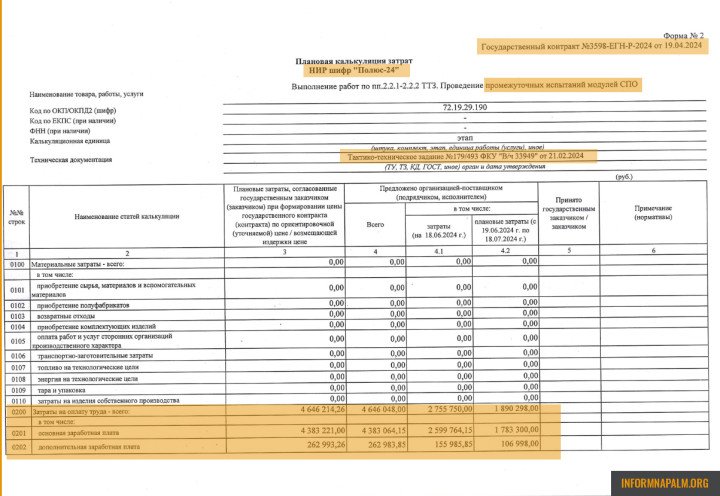
According to InformNapalm, the obtained documents include materials related to a research project code-named “Polyus-24,” which concerns intermediate testing of modules used in systems connected to Russia’s strategic nuclear forces. The documents indicate that the technical assignment for the project originated from Russian military unit 33949.
Open-source registry data reviewed by InformNapalm identifies the entity as Federal State Institution “Military Unit 33949,” registered in Moscow in 1993 and associated with activities related to military security.
According to InformNapalm, several independent investigations have linked this unit to Russia’s Foreign Intelligence Service (SVR), particularly operations connected to illegal intelligence networks abroad.
The documents also reference the organization “ANO TsP SYS AVN,” which the report describes as a structure connected to Russia’s strategic nuclear forces sector.

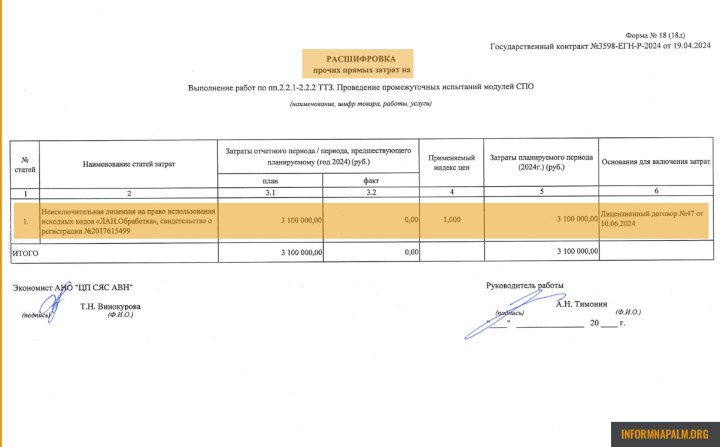
The materials include references to the technical task for the project, work stages, labor cost estimates, and licensing for third-party software components used during development.
The documentation indicates that the project involved 22 specialists and approximately 5,239 labor hours, with a total project value of roughly 11 million rubles (about $120,000), according to InformNapalm.
The cost structure included salaries, insurance payments, administrative expenses, and other direct operational costs, suggesting the work involved software development and analytical modeling rather than equipment procurement.
The documents also reference the licensed use of a software product called “LAN.Obrabotka,” described in open sources as a platform designed for multi-stage data processing and analysis, including data extraction, OCR, ETL processes, and modular architecture for large-scale information processing. The reference to this software component provides insight into technological tools used in the project.
Combining project documentation with open-source registry data allowed analysts to reconstruct connections between research programs, contractors, and Russian military structures involved in strategic systems development.
The investigative community noted that only part of the documents has been made public. Additional materials remain undisclosed to prevent exposing operational sources or methods.
The investigation follows previous disclosures by the intelligence community InformNapalm involving Russia’s defense sector. In November 2025, InformNapalm and the cyber center Fenix published classified documents from the Russian defense company OKBM related to the development of the PAK DA strategic stealth bomber and components for the Su-57 fighter jet.
Discuss this article:
-4a56a6b482ec132402c16ef6fcabf9a2.png)


-c439b7bd9030ecf9d5a4287dc361ba31.jpg)


